Documentation Index
Fetch the complete documentation index at: https://docs.getprimo.com/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
- A Microsoft account with administrator access to an Entra tenant
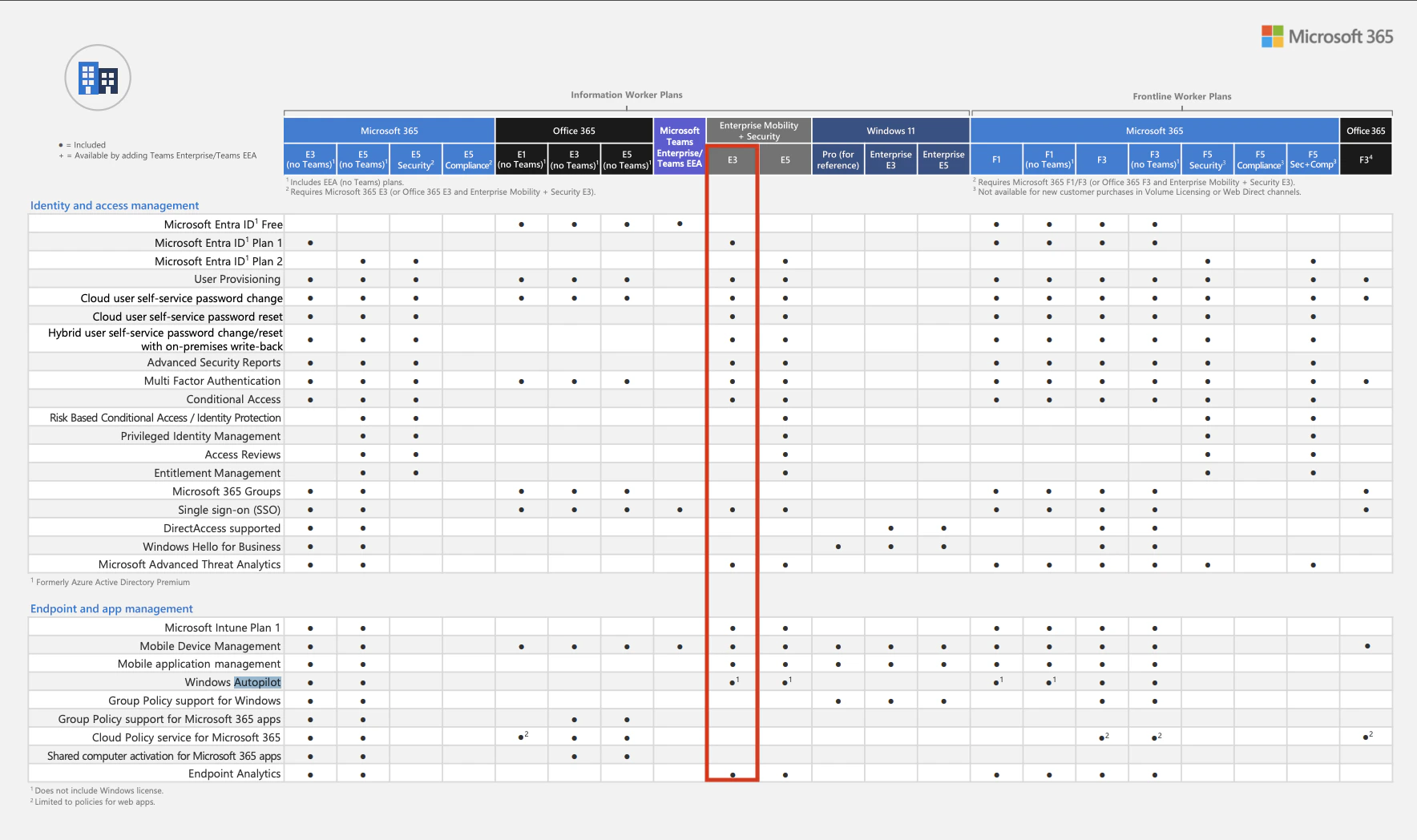
- A license that includes Microsoft Entra ID Plan 1 (or Plan 2) & Windows Autopilot
Restrictions
Autopilot devices use Entra accounts rather than local accounts. Microsoft is progressively deprecating local accounts in favor of Entra accounts. The Entra administrator can configure whether users have standard or administrator account privileges. Entra users with the Global Administrator role are automatically administrators on all Autopilot devices they sign into. Internet access is required during the first boot to authenticate with Entra.How to set it up
Declare the Fleet domain
This step requires coordination with Primo support. Microsoft generates a verification code that must be shared with the Primo team. Allow up to 2 business days for us to validate the code once it has been sent.
- Sign in to Microsoft Azure with an administrator account.
- Open Domain names and click + Add custom domain.
- Enter
{company}.mdm.getprimo.com. Contact support if you don’t know your domain. - Share the Destination or routing address value (format:
MS=ms12345678) with the Primo team, then wait for our confirmation before clicking Verify.
Create the Fleet application
-
Go to Mobility (MDM and MAM) and click + Add application > + Create your own application. Enter
Primoas the name and click Create. -
Fill in the MDM URLs and click Save:
Replace
{company}with your slug -
Open the Fleet application > Custom MDM application settings > click the link under Application ID URI > Edit > enter
https://{company}.mdm.getprimo.com> Save.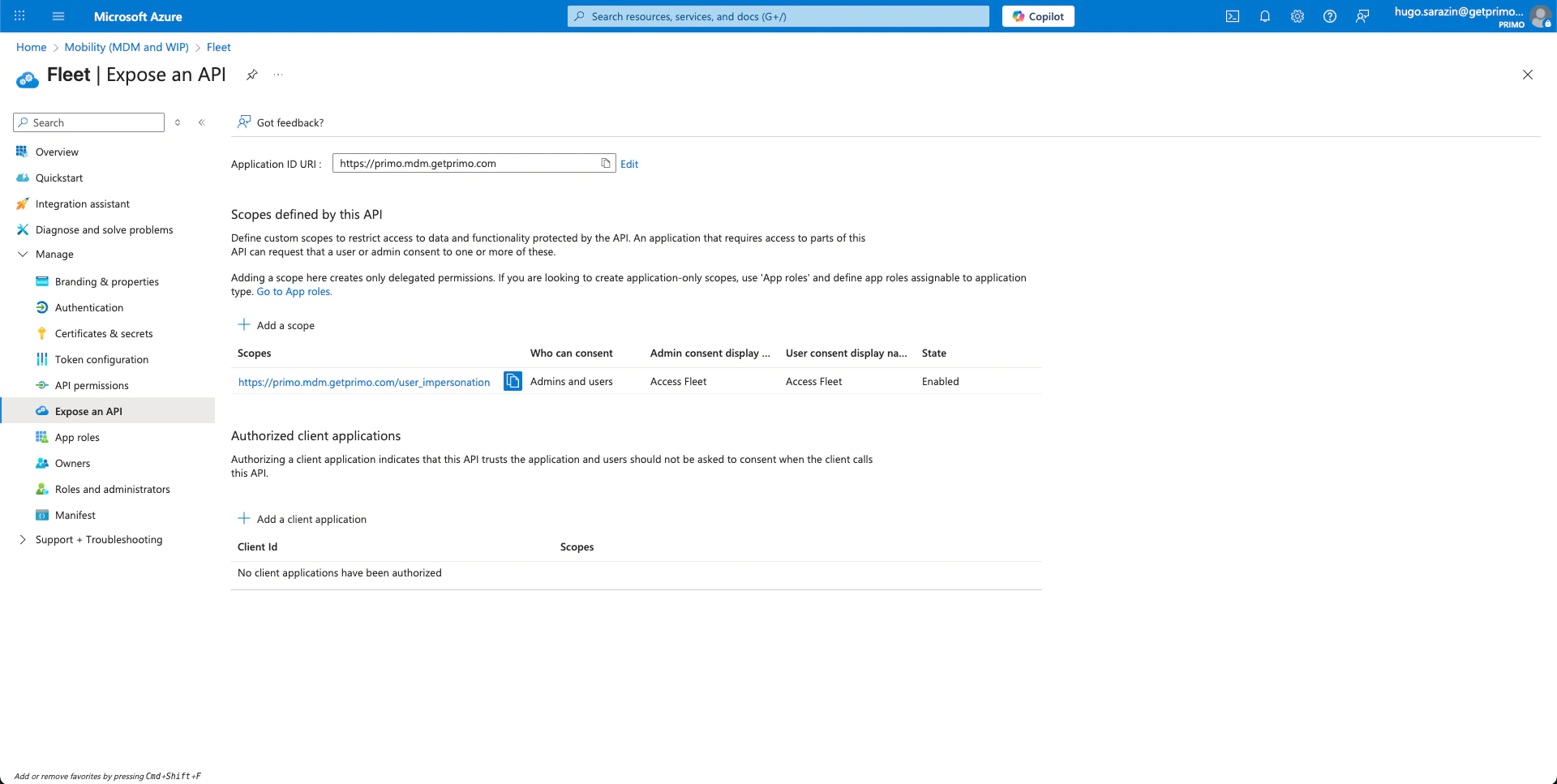
-
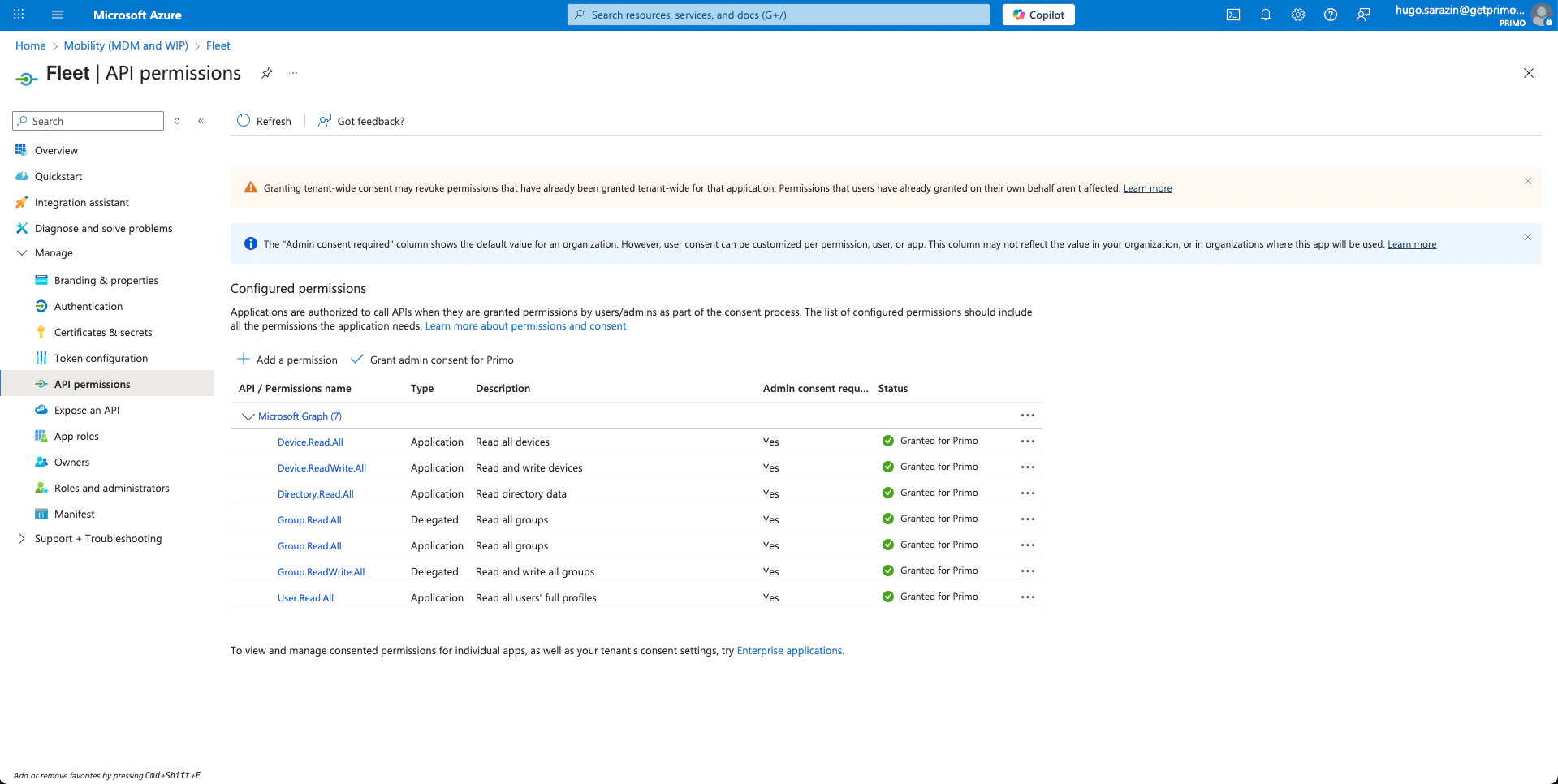
Go to API permissions > Add a permission > Microsoft Graph > Delegated permissions and add:
-
Add another permission under Application permissions:
-
Click Grant admin consent for {Your Company}.
Set Fleet as the default MDM for new devices
- Go to Mobility (MDM and MAM).
- Click Microsoft Intune > set MDM user scope and MAM user scope to
None> Save. - Click Fleet > set MDM user scope and MAM user scope to
All> Save.
Create Autopilot deployment profiles
A deployment profile defines the default settings of devices that enroll through Autopilot, such as
- user account type (Administrator or Standard)
- default country and keyboard language
- device naming pattern (e.g.
{company}-%RAND:5%→{company}-23456)
- Create the profile — go to Intune admin center > Devices > Enrollment > Deployment Profiles > + Create profile and complete the three steps: name, deployment mode, assignment.
- Create a dynamic device group — go to portal.azure.com > + Create group, name it (e.g. “Windows Autopilot devices”), select
Dynamic devices, and use the rule: - Create an Enrollment Status Page — go to Intune admin center > Devices > Enrollment > Enrollment Status Page > + Create, name the profile, enable progress display, and assign it to your dynamic group.